Security & Risk Leaders
Reduce access risk without slowing the business
Anugal gives security and risk leaders continuous control over who has access to what, ensuring identity risk is governed, provable, and aligned with business reality.
The Reality Security & Risk Leaders Face
Access risk doesn’t come from a single failure. It accumulates quietly through workforce change, exceptions, integrations, and approvals made without full context.
As organizations scale, access decisions increase in volume and urgency. Security teams are expected to prevent breaches, satisfy audits, and support business velocity often with fragmented controls and delayed visibility.
When incidents or audits occur, the question is no longer what happened, but why access was allowed in the first place. Anugal is built to answer that question continuously.
Where Access Risk Escapes Control
Even mature organizations struggle with the same exposure points.
Access Drift
Permissions remain after responsibilities change. Users accumulate entitlements across applications and platforms.
Late Policy Detection
Segregation of Duties conflicts and eligibility violations are identified after access is active.
Fragmented Authorization
Requests are approved without preserved context, defined ownership, or validated justification.
Certification Fatigue
Managers review technical entitlements without business clarity, reducing the reliability of decisions.
Reactive Audit Evidence
Logs exist across systems, but governance proof must be reconstructed manually.
Where Anugal Fits in Your Risk Strategy
Anugal strengthens identity governance as a foundational layer in your security architecture ensuring access decisions are controlled, measurable, and aligned with risk policy.

- Identity as a core security control plane
- Preventive access risk management aligned to Zero Trust principles
- Continuous regulatory and audit assurance
- Cross-system governance orchestration across SAP, SaaS, cloud, and legacy environments
- Sustainable least-privilege enforcement at enterprise scale
Anugal’s Approach: Govern Every Access Change Before It Executes
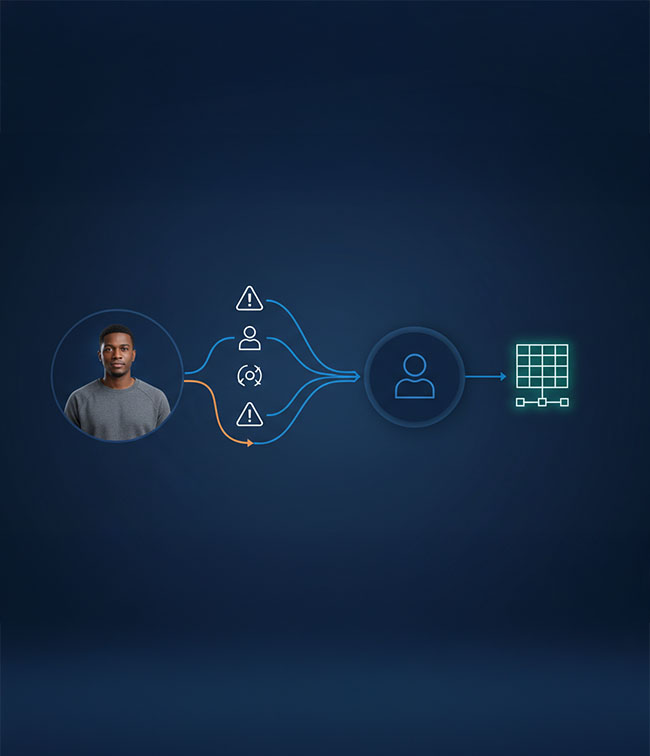
Anugal ensures access does not go live unless it has passed governance. Every access change whether triggered by HR, requested by a user, initiated for a vendor, or granted as emergency access flows through structured control gates:
- Policy & Eligibility Validation
Access is checked against entitlement
rules, role eligibility, and baseline
constraints. - SoD & Risk Enforcement
Conflicts and risky combinations are detected and blocked or escalated before approval. - Ownership-Based Authorization
Requests are routed to accountable access owners with preserved context and justification. - Decision Traceability by Design
Every decision records who approved it, under what policy, and with what risk outcome.

What Security & Risk Leaders Gain
Continuous Access Integrity
Access remains aligned to role, eligibility, and purpose as users move, change, or exit across systems and organizational structures.
Preventive Policy Enforcement
SoD conflicts and policy violations are blocked before execution through automated validation and governance-driven approval controls.
Accountable Authorization Decisions
Approvals are traceable, contextual, and defensible with preserved business justification and policy evaluation context.
Audit-Ready Governance
Evidence is generated automatically as decisions occur, eliminating manual reconstruction during audits or compliance assessments.
Governed Privileged & Vendor Access
Emergency and third-party access follow structured, time-bound controls with enforced ownership and continuous monitoring.
Real-Time Risk Visibility
Security teams gain measurable exposure insights across employees, vendors, and machine identities in real operational environments.



