Retail
Operational Identity Governance Across Stores, Warehouses, and Digital Commerce
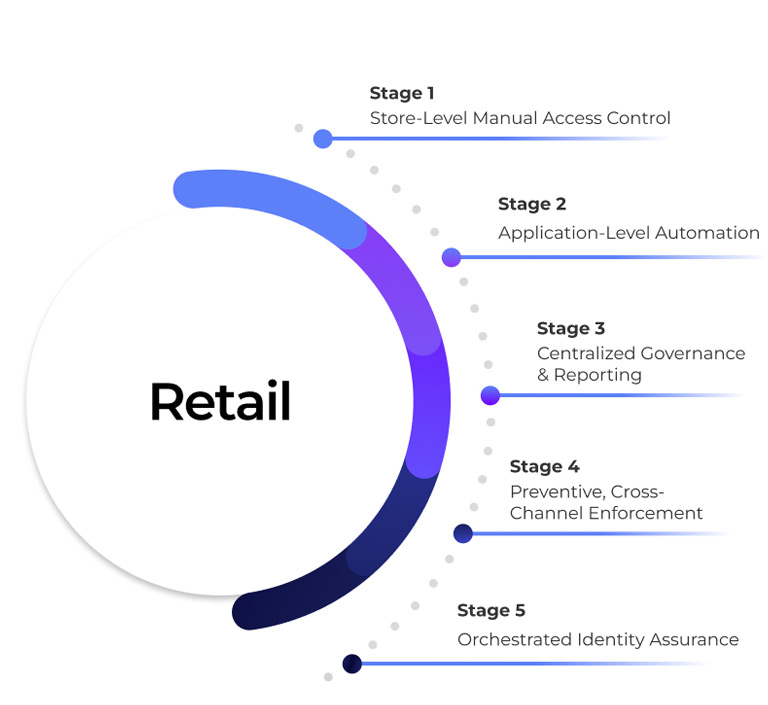
Enforcing Access Control Across Physical and Digital Retail Systems

The Reality of Access Risk in Retail
Behind every POS transaction, inventory update, supplier payment, and online order lies identity in motion. Across retail enterprises, identity operates across stores, e-commerce platforms, warehouses, ERP systems, and third-party logistics, often across a highly distributed workforce.
Retail teams rotate shifts, seasonal staff onboard quickly, and transactions move at high velocity. Yet access updates don’t always keep pace. Role changes lag, temporary access persists, and cross-system permissions fall out of sync between physical and digital operations. These are not minor inefficiencies. In a high-volume retail environment, delayed revocation or excessive access directly increases fraud exposure, revenue leakage, and compliance risk.
The Core Challenges Retail Organizations Face
High Workforce Turnover & Seasonal Scale
- Retail operates with store associates, warehouse staff, temporary workers, franchise operators, and seasonal hires.
- Manual Joiner–Mover–Leaver processes cannot keep pace with frequent onboarding and offboarding.
- Access granted during peak seasons often remains active long after employment ends, creating dormant access risk.
Distributed Systems Across Physical & Digital Channels
- Retail environments combine POS systems, inventory platforms, ERP, CRM, loyalty systems, and e-commerce applications.
- A single over-privileged identity can impact pricing, refunds, inventory adjustments, or supplier payments.
- Fragmented governance across stores and digital platforms increases fraud and data exposure risk.
Segregation of Duties in Financial & Operational Workflows
- In retail ERP systems, users may create vendors, process returns, approve discounts, and reconcile payments.
- Conflicting access combinations are often identified after financial discrepancies occur.
- Without preventive SoD enforcement, fraud risk becomes revenue leakage.
Compliance & Data Protection Pressure
- Retailers must align with PCI-DSS, GDPR, regional privacy laws, and financial reporting standards.
- Customer payment data and loyalty information require continuous protection.
- Traditional IGA produces compliance reports but lacks preventive enforcement across fast-moving retail operations.


Why Traditional IGA Falls Falls Short for Retail
Most IGA platforms were designed for stable corporate structures and predictable workforce models.
Retail requires:
- Rapid onboarding and offboarding
- Store-level access governance
- Time-bound seasonal access control
- Cross-platform orchestration across POS, ERP, and e-commerce
- Continuous enforcement at scale

What Orchestrated Identity Enables in Retail
-
Lifecycle Governance
-
Preventive Control
-
SoD Enforcement
-
Third-Party Governance
-
Risk Intelligence

Lifecycle- Governed Workforce Access
When HR or employment status changes:
- Access across POS, ERP, warehouse, and digital systems updates automatically.
- Obsolete permissions are removed immediately.
- Store-specific and role-based access remain aligned to operational responsibility.
No lingering seasonal access. No manual cleanup. No hidden risk.

Preventive Privileged Access Control
Orchestration enforces:
- Purpose-based administrative access
- Time-bound privilege elevation
- Automatic revocation post-task
- Full decision traceability across systems
Sensitive retail systems remain protected, even during peak operations.

Continuous Segregation of Duties Enforcement
Instead of identifying fraud after loss:
- SoD risks are evaluated at request time.
- Conflicting combinations in pricing, vendor management, and refunds are blocked before approval.
- Mitigations are enforced dynamically.
Revenue risk is prevented, not reconciled later.

Third-Party & Franchise Identity Governance
Retail relies heavily on Logistics providers, Franchise operators, Merchandising partners and Technology vendors. Orchestrated governance ensures:
- Time-bound, location-specific access
- Automatic expiry aligned to contracts
- Clear business sponsorship
- Audit-ready lifecycle evidence
No dormant third-party access in customer or financial systems.

Continuous Identity Risk Intelligence
Advanced orchestration enables:
- Detection of unusual refund or pricing behavior
- Identification of privilege creep across store roles
- Automated remediation triggers
- Escalation of access anomalies with preserved context
Identity risk becomes measurable across physical and digital retail environments.
Why This Matters to Retail Leadership

Reduced fraud and revenue leakage

Lower insider threat exposure

Stronger PCI and privacy compliance posture

Fewer audit findings related to access control

Clear accountability for access decisions across stores and digital platforms



