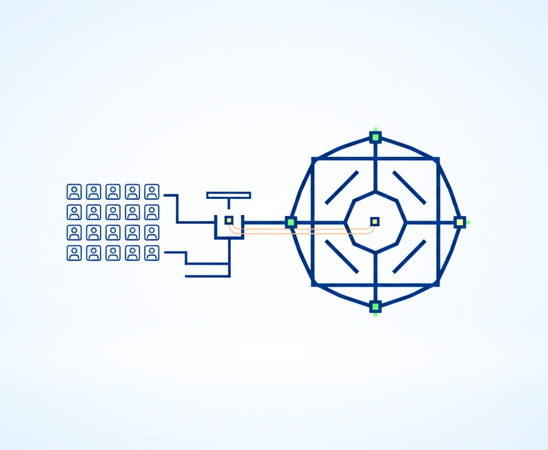
Mass & Bulk Access Requests
Roll out access at scale without losing approval control
Anugal enables controlled bulk access provisioning that preserves ownership and traceability so speed never compromises governance.

Execute bulk access changes without losing governance or audit control
Large-scale access changes are common during go-lives, migrations, restructures and project onboarding. Yet bulk provisioning is often handled through scripts or urgent approvals that bypass policy checks thus creating access sprawl.
Anugal governs mass access requests as controlled authorization events. Bulk access is approved by the right owners, validated against policy before execution, and fully traceable at the individual level—allowing enterprises to move fast while maintaining control, accountability, and audit readiness.
The problem enterprises face
Bulk access changes create hidden governance gaps

Uncontrolled mass provisioning
Access is granted in bulk using scripts or spreadsheets without clear authorization.
Approval shortcuts under delivery pressure
Governance is bypassed to meet project timelines.
Limited traceability
Auditors cannot link bulk access to individual justification or approval.
Post-go-live access sprawl
Temporary project access becomes permanent standing access.
How Anugal govern bulk access requests?
Anugal treats bulk access as a governed authorization event, not a technical shortcut. Every mass request is policy-validated, approved by the right owners, executed with orchestration, and recorded with full audit evidence thus ensuring scale without loss of control.
Controlled Bulk Access Provisioning
Bulk access is issued with the same rigor as individual requests.
- Supports bulk access for projects, rollouts, and go-lives
- Applies standardized access models instead of free-form lists
- Prevents unmanaged spreadsheet-driven provisioning
- Ensures consistency across all affected identities

Approval & Ownership Governance
Approval paths adapt to access risk.- Approval routed to application and role owners
- Project-based access requires explicit sponsorship
- Sensitive access triggers additional authorization layers
- Prevents mass approval without accountability
Policy Enforcement at Scale
Governance rules apply even during bulk operations.
- Eligibility and SoD checks enforced before execution
- Ineligible users excluded automatically
- Prevents policy violations during high-volume changes
- Reduces post-provisioning remediation effort


Traceability & Audit-Ready Reporting
Every bulk action is fully explainable.
- Records who approved, what was granted, and why
- Maintains per-user access evidence within bulk events
- Enables audit review without manual reconstruction
- Simplifies compliance reporting for large initiatives
How Access Requests Become Defensible Authorization Decisions
Access requests in Anugal progress through a governed decision model that evaluates eligibility and risk before approval, ensuring only justified access is executed.
Joiner Automation
- Access is provisioned directly from HR role and position data
- Employees start productive from day one without manual access requests
- Governance controls are enforced before any access is granted
- Access decisions are logged and traceable from the outset
Outcome:Faster productivity with controlled access
Mover Automation
- Access is recalculated whenever roles, departments, or locations change
- Excess and legacy entitlements are removed automatically
- Access reflects current responsibility, not historical roles
- Changes are governed and recorded as part of normal operations
Outcome: Continuous access alignment as roles evolve
Leaver Automation
- All user and privileged access is revoked immediately upon termination
- Orphaned and standing access is eliminated across systems
- Deprovisioning actions are consistent and verifiable
- Offboarding evidence is generated automatically
Outcome: Risk-free exits and audit-ready offboarding
Business impact of Anugal

Faster project onboarding without bypassing governance

Reduced IT effort managing manual bulk provisioning

Lower risk of excessive or unintended access

Clear, defensible audit evidence for large-scale changes

Fewer audit findings related to project and rollout access



