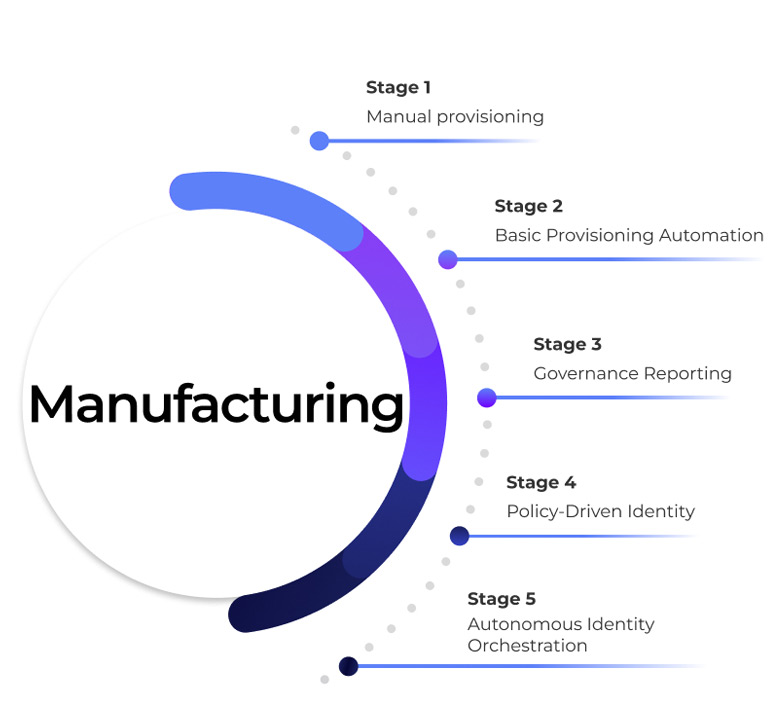
Manufacturing
Secure identity across plant operations without disrupting production
How Orchestrated Identity Governance Is Transforming Modern Manufacturing

The Reality of Access Risk in Manufacturing
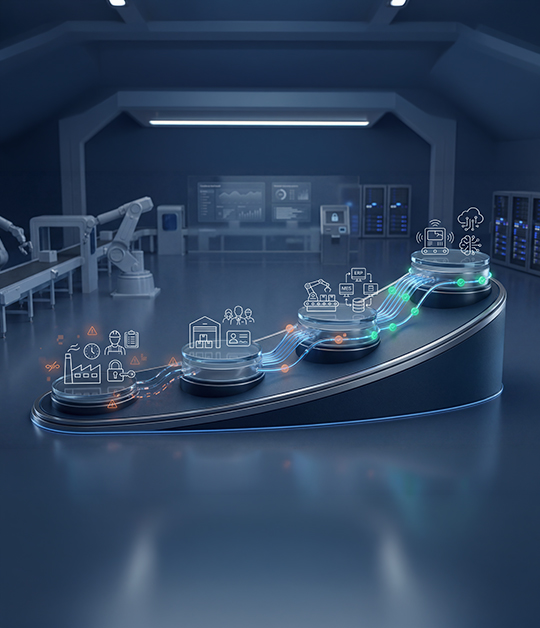
Behind every production run, ERP transaction, quality check, and connected machine command lies identity in motion. Across manufacturing environments, identity must operate consistently across IT systems, Operational Technology (OT), plant applications, engineering tools, vendor networks, and legacy platforms.
Yet access execution rarely matches operational tempo. Role updates fail to align with shift rotations and cross-functional assignments. Temporary contractor, maintenance, or integrator access remains active beyond approved work windows. Permissions granted in corporate IT environments do not always synchronize accurately with plant or OT systems.
In manufacturing, delayed revocation, excessive privilege, or inconsistent cross-system enforcement can interrupt production and weaken supply chain reliability. In modern factories, identity is infrastructure and it must perform with the same discipline as production systems themselves.
The Core Challenges Manufacturing Organizations Face
Workforce Mobility at Production Scale
- Manufacturing environments rely on shift workers, plant transfers, contractors, seasonal labor, and external maintenance vendors.
- Manual Joiner–Mover–Leaver processes cannot keep pace with plant-level access changes.
- Access granted during onboarding often remains active across role changes or site transfers, creating silent operational risk.
IT–OT Convergence Risk
- ERP systems integrate with MES, SCADA, PLC systems, and IoT platforms.
- A single over-privileged identity can move from IT systems into operational technology environments.
- Compromised access in OT is not just a data risk—it is a production shutdown risk.
Segregation of Duties in Complex ERP Landscapes
- In manufacturing ERP systems, users may create vendors, approve purchase orders, post invoices, and release payments.
- Conflicting access combinations are often identified during audits—not prevented during access requests.
- Without preventive SoD enforcement, fraud and financial manipulation risk becomes operational exposure.
Regulatory & Compliance Pressure
- Manufacturers face SOX, ISO 27001, NIS2, industry safety standards, and supply chain compliance requirements.
- Auditors expect continuous control evidence across ERP, plant systems, and third-party access.
- Traditional IGA generates reports but does not orchestrate real-time enforcement across IT and OT environments.


Why Traditional IGA Falls Falls Short for Manufacturing
Most IGA platforms were built for static corporate environments and office-based workforces.
Manufacturing requires:
- Real-time provisioning aligned to plant shifts
- OT-aware access governance
- Contractor lifecycle control
- Cross-system orchestration across ERP and operational platforms
- Continuous enforcement, not periodic review
What Orchestrated Identity Enables in Manufacturing
-
Lifecycle governance
-
Preventive control
-
SoD Enforcement
-
Third-Party Governance
-
Risk Intelligence

Lifecycle- Governed Workforce Access
When HR or plant assignments change:
- Access across ERP, MES, and plant systems updates automatically.
- Obsolete permissions are removed immediately.
- Shift-based and role-based access remain aligned to production responsibility.
No tickets. No delays. No residual plant-level access risk.

Preventive IT–OT Privileged Access Control
Orchestration enforces:
- Purpose-specific privileged access
- Time-bound elevation in critical systems
- Automatic revocation post-task completion
- Full decision and execution traceability
Privileged access becomes controlled, not assumed.

Continuous Segregation of Duties Enforcement
Instead of discovering violations during audit cycles:
- SoD risks are evaluated at request time.
- Conflicts across ERP and financial modules are blocked before approval.
- Mitigations are enforced dynamically.
Risk is prevented, not documented later.
Third-Party & Vendor Identity Governance
Manufacturing depends on equipment vendors, integrators, and maintenance contractors.
Orchestrated governance ensures:
- Site-specific, time-bound access
- Automatic expiration aligned to contracts
- Clear business ownership
- Audit-ready lifecycle evidence
No dormant vendor access inside production systems.

Continuous Identity Risk Intelligence
Advanced orchestration enables:
- Detection of unusual plant access behavior
- Identification of privilege accumulation across shifts
- Automated remediation triggers
- Escalation of operational risk with preserved context
Identity risk becomes visible across both IT and OT layers.
Why This Matters to Manufacturing Leadership

Reduced risk of production disruption

Lower exposure to vendor-driven breaches

Stronger ERP and financial control integrity

Improved regulatory posture

Clear accountability for access decisions across plants



