Banking & Financial Services (BFSI)
Control access risk across complex financial operations without slowing the business
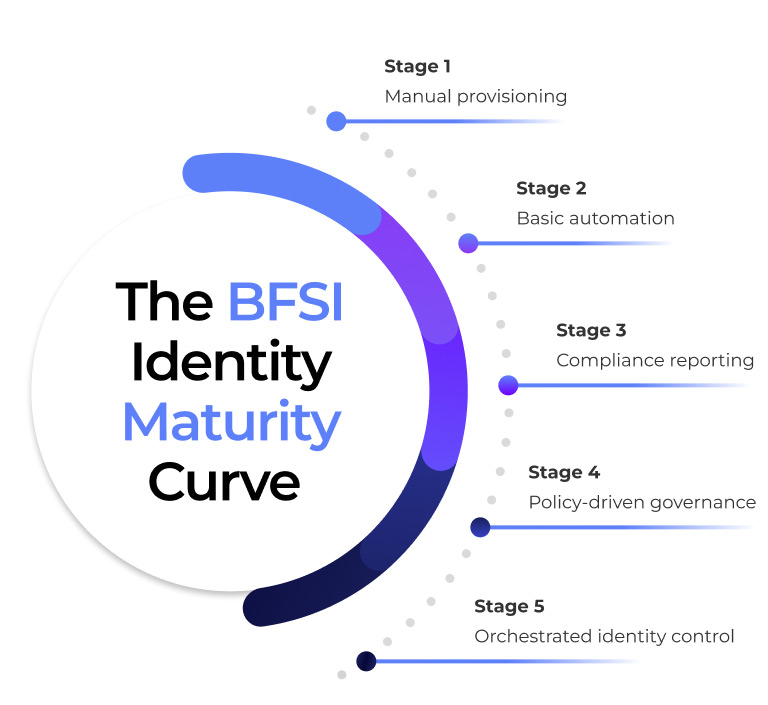
Orchestrated Identity Governance Is Reshaping BFSI

The Reality of Access Risk in the Finance Sector
Behind every transaction posting, payment approval, trading action, and customer interaction lies identity in motion. Across banks and financial institutions, that identity must execute consistently across core banking systems, payment platforms, treasury tools, risk engines, and customer applications.
Yet access changes rarely move at operational speed. Role updates lag behind team transfers and shift rotations. Temporary or project-based access remains active beyond its intended duration. Cross-system provisioning gaps create mismatches—where access is approved in one system but persists or fails to update in another.
These are not isolated IT inefficiencies. They are execution gaps. In financial environments, delayed revocation, excessive privilege, or inconsistent enforcement across systems directly increases fraud exposure, regulatory risk, and reputational damage.
The Core Challenges BFSI Organizations Face
Most organizations have JML processes but they are operationally weak.
Workforce Mobility at Financial Scale
- Continuous internal role rotations, cross-functional projects, and temporary assignments create constant access movement.
- Manual Joiner–Mover–Leaver processes fail to keep pace with real-time workforce changes.
- Access granted during onboarding often persists across role changes, increasing silent risk exposure.
Regulatory & Audit Strain
- Privileged identities span core banking, payment systems, treasury platforms, and sensitive data environments.
- Over-privileged accounts can bypass layered security controls across interconnected financial systems.
- A single compromised privileged identity can trigger systemic financial, operational, and reputational damage.
Segregation of Duties Under Pressure
- Users in complex financial systems may initiate, approve, and reconcile transactions within the same workflow.
- SoD conflicts often surface during audits rather than at the point of access request.
- Without preventive enforcement, fraud risk shifts from theoretical compliance gap to operational reality.
Privileged Access as a Breach Vector
- BFSI institutions must align with SOX, GDPR, PCI-DSS, NIST, and region-specific banking mandates.
- Regulatory scrutiny demands provable, decision-level audit evidence—not just activity logs.
- Traditional IGA generates reports but lacks real-time policy enforcement and preventive control.


Why Traditional IGA Falls Short for BFSI
Most IGA platforms were built for static roles, periodic reviews, and ticket-driven provisioning.
BFSI requires:
- Real-time access decisions
- Preventive policy enforcement
- Ownership-based approvals
- Continuous audit readiness
- Cross-system orchestration
- Time-bound access controls

What Orchestrated Identity Enables in BFSI
-
Lifecycle Governance
-
SoD Enforcement
-
Preventive control
-
Third-Party Governance
-
Risk Intelligence

Lifecycle-Governed Workforce Access
When HR or identity attributes change:
- Access across banking systems updates automatically
- Obsolete permissions are removed immediately
- Birthright and role-based access remain aligned to responsibility
No tickets.
No delays.
No residual access risk.

Continuous Segregation of Duties Enforcement
Instead of discovering violations during audits:
- SoD risks are evaluated at request time
- Conflicts are blocked before approval
- Mitigations are enforced dynamically
Risk is prevented, not documented later.

Preventive Privileged Access Control
Orchestration enforces:
- Purpose-based privileged access
- Time-bound elevation
- Automatic revocation
- Full session and decision traceability
Privileged access becomes controlled not assumed.

Third-Party & Vendor Identity Governance
Financial institutions rely heavily on external providers.
Orchestrated governance ensures:
- Time-bound, purpose-specific access
- Automatic expiry and revocation
- Clear sponsorship and ownership
- Audit-ready lifecycle evidence
No more dormant vendor access in critical systems.

Continuous Identity Risk Intelligence
Advanced orchestration enables:
- Detection of unusual access patterns
- Identification of privilege creep
- Automated remediation triggers
- Risk escalation with preserved context
Identity risk becomes visible, measurable, and actionable.
Why This Matters to BFSI Leadership

Lower exposure to access-driven fraud

Reduced insider threat impact

Stronger regulatory posture

Fewer audit findings tied to identity

Clear accountability for access decisions



