Approval & Access Control Engine
Eliminate untraceable access approvals across your entreprise
Anugal ensures every approval decision is deliberate, policy-enforced and owned hence access is granted only when it is justified.

Every access approval is a governed authorization decision with explicit accountability
As enterprise environments scale, access approvals increase in both volume and urgency. What should function as deliberate authorization decisions are often reduced to routine workflow actions executed under time pressure.
Approval authority is misaligned, decision context is limited, and governance checks are applied inconsistently or too late. The result is a growing gap between approved access and defensible authorization, which becomes visible during audits, investigations, and security incidents.
Where Approval Governance Breaks
Approvals exist in most enterprises, but authorization control is fragmented, informal, and insufficient to withstand audit or risk scrutiny.

Hierarchy-driven approvals
Access is approved based on reporting lines rather than true ownership or access impact.
Limited decision context
Approvers lack visibility into what access enables, its risk level, or policy implications.
Policy checks applied too late
Eligibility, SoD, and risk violations are often detected after access is provisioned.
Non-defensible audit records
Approval logs show who clicked “approve,” but not why access was permitted.
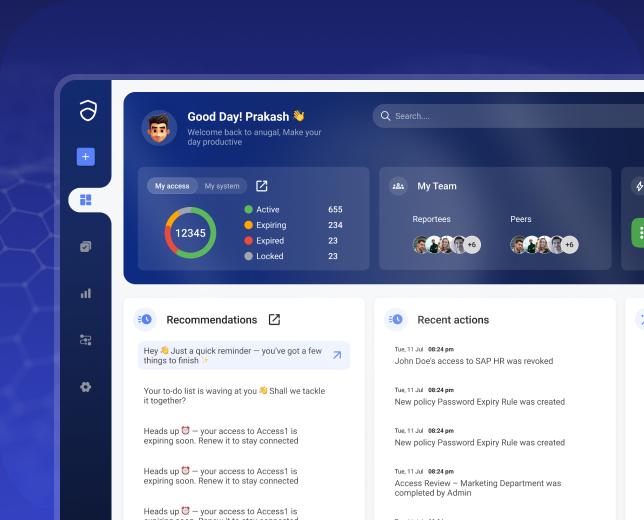
How Anugal approach approvals?
Anugal governs approvals as authorization decisions, not workflow tasks. Approval authority is dynamically determined based on access type, sensitivity, and ownership, while governance rules are evaluated before approval routing occurs. This ensures only eligible, policy-compliant access ever reaches an approver, and every approval is backed by enforceable justification.
Ownership-Based & Delegated Approvals
Approval authority is aligned to real access ownership.
- Routes approvals to application, data, or role owners
- Prevents approvals by uninformed or unrelated managers
- Supports delegation without breaking accountability
- Preserves ownership clarity for audit and review
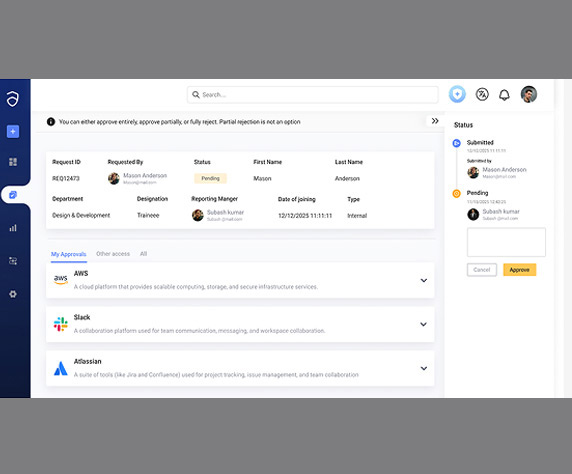
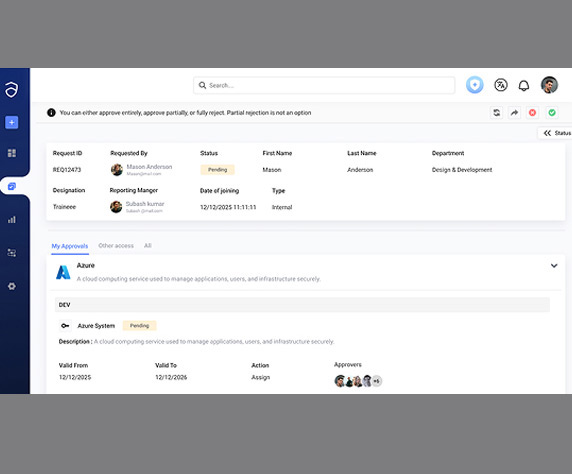
Conditional & Multi-Level Approval Routing
Approval paths adapt to access risk.
- Dynamically routes approvals based on role and sensitivity
- Triggers additional approval layers for high-risk access
- Supports parallel and sequential approval models
- Prevents blanket approvals for sensitive entitlements
Policy-Enforced Authorization Controls
Governance rules are applied before approval decisions.
- Evaluates eligibility, SoD, and risk at request time
- Blocks ineligible access before reaching approvers
- Ensures approvals cannot override policy violations
- Reduces post-provisioning remediation effort
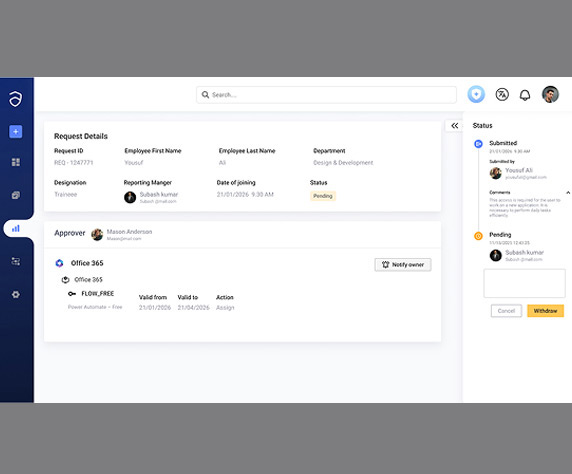
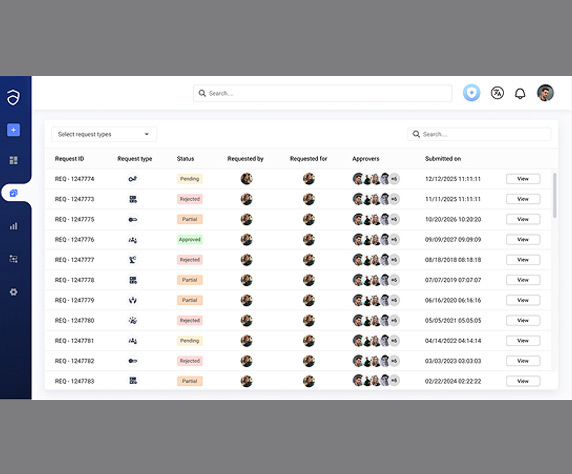
Approval Decision Traceability
Every approval is recorded as a defensible decision.
- Captures who approved, under which policy, and why
- Preserves decision context beyond access provisioning
- Provides clear evidence for audits and investigations
- Reduces audit clarification and follow-up cycles
Business impact of Anugal

Fewer inappropriate access approvals

Reduced need for post-provisioning corrections

Stronger accountability for access decisions

Clear, defensible audit evidence by default

Lower audit findings related to weak authorization
How Access Requests Become Defensible Authorization Decisions
Access requests in Anugal progress through a governed decision model that evaluates eligibility and risk before approval, ensuring only justified access is executed.
Governed Request Intake
- Requests initiated through a controlled entry point
- Identity context, access scope, and target systems captured
- Access type classified (role, entitlement, privilege)
Pre-Authorization Policy & Risk Evaluation
- Eligibility rules and access policies evaluated before approval
- SoD conflicts and excessive privilege assessed
- Contextual risk signals applied at decision time
Accountable Approval Decision
- Approved access is provisioned across target systems through governed execution
- Provisioning follows defined scope, role constraints, and access boundaries
- Execution steps are logged with identity, system, and approval context
Controlled Access Execution
- Approved access provisioned through governed orchestration
- Execution follows defined scope and sequencing
- Actions logged with identity and system context