Access Certifications
Certify every access and avoid audit risks at your firm
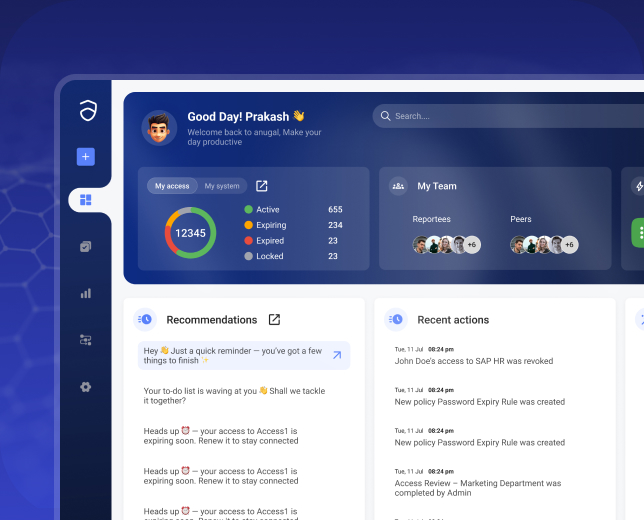
Anugal enforces periodic, ownership-based access reviews that remove excess access, sustain least privilege, and produce audit-ready evidence by default.

Prove access is still correct every time auditors ask
As organizations grow, access expands silently. Users change roles, projects end, contractors rotate, and emergency access lingers longer than intended. Without structured certification, outdated and excessive access remains in place, often unnoticed by operations.
Audits then expose what daily processes missed: stale entitlements, rubber-stamped approvals, missing justification, and remediation that cannot be proven. The issue is not that reviews were skipped, but that certifications were never enforced as control mechanisms.
Where Access Reviews Break
Most enterprises perform reviews but not effective certifications.

Spreadsheet-driven campaigns
Manual exports, emails, and offline tracking fail to scale or withstand audits.
Wrong reviewers, wrong decisions
Managers lack entitlement and risk context; owners are not involved.
Low completion and follow-through
Reviews stall, escalations are manual, and revocations are delayed.
Weak audit evidence
Approvals exist, but justification, timestamps, and remediation proof are missing.
How Anugal approaches access certifications
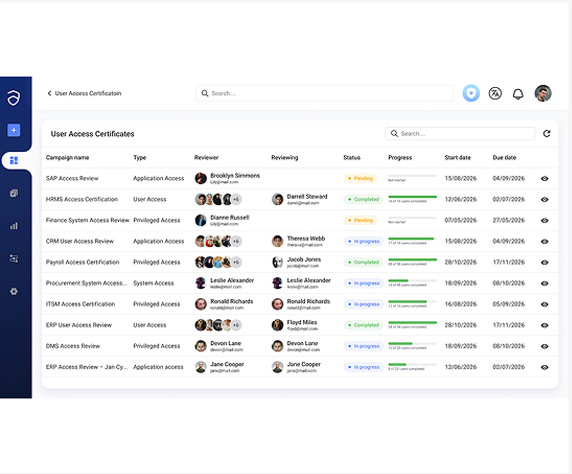
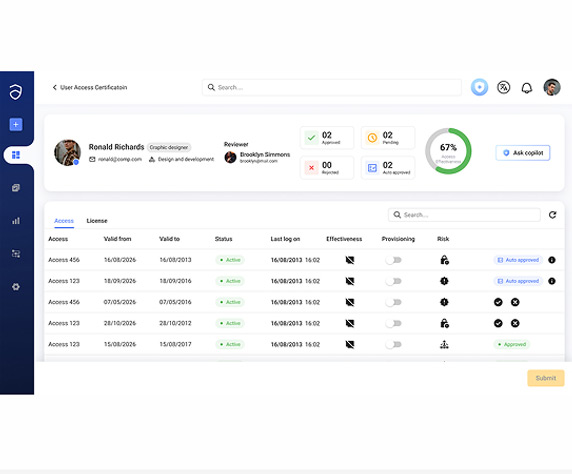
Anugal treats certifications as continuous governance controls, not periodic checklists. Review campaigns are orchestrated end-to-end assigning the right reviewers, surfacing risk context, enforcing justification, automating remediation, and preserving immutable audit evidence.
Ownership-Based Review Campaigns
Access is validated by those who understand its impact.
- Routes reviews to managers, application owners, and entitlement owners
- Aligns decisions to true access ownership
- Prevents uninformed rubber-stamping
- Strengthens accountability for approvals
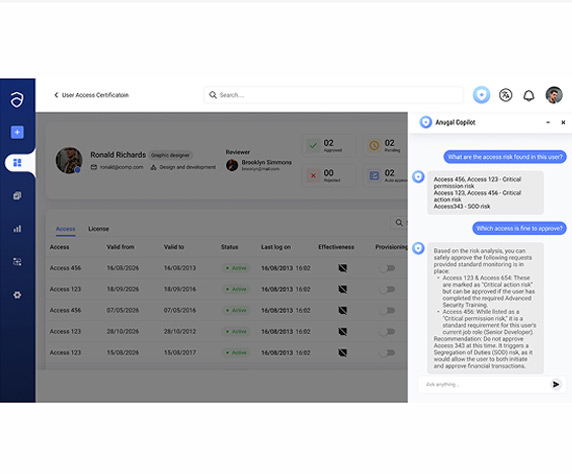
Context-Rich Review Decisions
Reviewers see risk not just access lists.
- Highlights privileged, dormant, and high-risk access
- Flags SoD conflicts and sensitive permissions
- Provides plain-language entitlement descriptions
- Improves decision accuracy and confidence
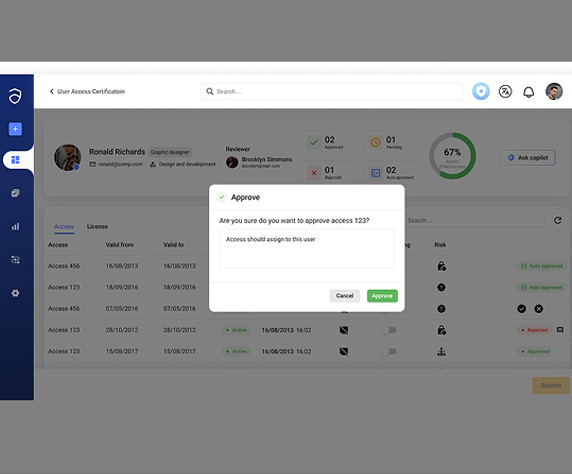
Automated Remediation & Enforcement
Decisions translate directly into action.
- Revokes rejected access automatically
- Enforces remediation SLAs
- Eliminates manual IT follow-ups
- Prevents access drift post-review
Audit-Ready Certification Evidence
Every campaign produces defensible proof.
- Captures reviewer, decision, justification, and timestamp
- Preserves access state at time of review
- Tracks remediation outcomes
- Exports complete audit evidence packages
How Certifications Stay Continuous
Access certifications operate as recurring governance cycles.Campaign Scheduling
- Certification campaigns are scoped by role, application, entitlement type, or risk level
- Review frequency, timelines, and recurrence are defined centrally
- Ownership and accountability for each campaign are established
Ownership-based Review
- Reviews are routed to managers, application owners, or entitlement owners
- Ownership context is enforced for each access decision
- Escalation paths are defined for non-response or conflict
Risk-aware Decisions
- Reviewers see risk indicators, SoD conflicts, and privilege level
- Usage context and entitlement descriptions are presented clearly
- Justification is enforced for approvals, rejections, and exceptions
Automated Revocation
- Rejected access is revoked automatically across target systems
- Remediation actions are tracked through completion
- SLAs and deadlines are enforced for corrective actions
Immutable audit Evidence
- Decisions, actions, and outcomes are recorded as append-only evidence
- Records retain timestamps, actors, and governance context
- Evidence remains continuously available for audits and reviews
Business impact of Anugal

Removal of dormant and excess access at scale

Higher review completion rates with fewer escalations

Reduced audit findings related to access governance

Lower IAM and compliance workload

Continuous enforcement of least privilege