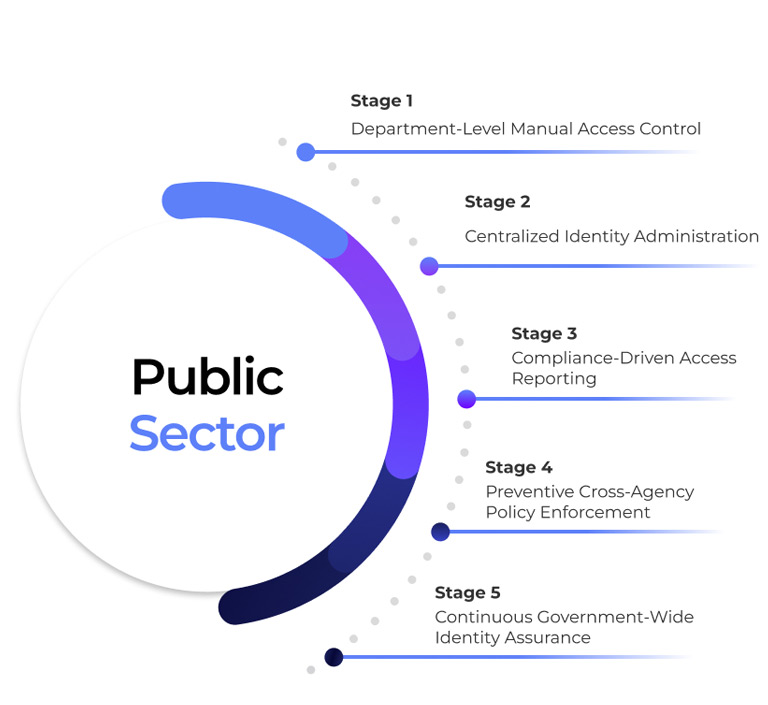
Public Sector
Strengthen citizen trust through controlled, transparent identity governance
How Orchestrated Identity Governance Is Modernizing the Public Sector

The Reality of Access Risk the Public Sector
Behind every citizen record, welfare disbursement, tax filing, public safety response, and digital service transaction lies identity in action. Across government departments and agencies, identity operates across legacy platforms, modern cloud systems, shared services, contractors, and inter-agency environments.
Role changes, temporary assignments, election cycles, and contractor engagements create constant access movement. Yet permissions often remain active beyond need, and updates fail to synchronize consistently across interconnected systems.
These are not minor administrative gaps. In the public sector, access is authority. When authority is not precisely governed and time-bound, it increases exposure to data misuse, compliance failures, security incidents, and erosion of public trust.
The Core Challenges Retail Organizations Face
Workforce Scale & Inter-Agency Mobility
- Government agencies operate across ministries, departments, field offices, and regional units.
- Frequent transfers, deputations, contract roles, and project-based assignments create constant access movement.
- Manual Joiner–Mover–Leaver processes struggle to keep pace, leaving dormant or excessive access behind.
Legacy System Fragmentation
- Public sector IT landscapes combine decades-old legacy systems with modern digital services.
- Access controls differ across departments and often lack centralized governance.
- Over-privileged identities can move laterally across interconnected systems without consistent policy enforcement.
Segregation of Duties in High-Impact Workflows
- Users may initiate, approve, and reconcile financial disbursements, grants, procurement actions, or citizen benefit approvals.
- SoD conflicts are frequently discovered during audits rather than prevented during access decisions.
- Without preventive enforcement, fraud and misuse risk increases within critical public programs.
Regulatory, Oversight & Audit Pressure
- Public institutions must comply with national data protection laws, financial accountability standards, cybersecurity frameworks, and oversight mandates.
- Auditors require defensible, decision-level evidence of access governance.
- Traditional IGA platforms produce reports—but often lack real-time enforcement and cross-department orchestration.


Why Traditional IGA Falls Short for the Public Sector
Many legacy IGA platforms assume centralized corporate environments with uniform systems. Public sector environments require:
Retail requires:
- Cross-agency lifecycle governance
- Policy enforcement across legacy and modern platforms
- Time-bound contractor and consultant access
- Continuous audit readiness
- Orchestration across departmental silos

What Orchestrated Identity Enables in the Public Sector
-
Lifecycle Governance
-
Preventive Control
-
SoD Enforcement
-
Third-Party Governance
-
Risk Intelligence

Lifecycle- Governed Workforce Access
When employment status, department, or assignment changes:
- Access across systems updates automatically.
- Obsolete permissions are removed immediately.
- Role-based access remains aligned to official responsibility.
No residual access across agencies. No manual reconciliation.

Preventive Privileged Access Control
Orchestration enforces:
- Purpose-based administrative access
- Time-bound elevation
- Automatic revocation after task completion
- Full decision and execution traceability
Privileged access becomes transparent and accountable.

Continuous Segregation of Duties Enforcement
Instead of identifying issues during oversight reviews:
- SoD risks are evaluated at request time.
- Conflicting combinations in finance, procurement, or benefit systems are blocked before approval.
- Mitigations are enforced dynamically.
Risk is prevented, not documented after exposure.

Contractor & Third-Party Identity Governance
Public agencies depend on consultants, technology providers, and service partners.
Orchestrated governance ensures:
- Time-bound, project-specific access
- Automatic expiry aligned to contracts
- Clear sponsorship within departments
- Audit-ready lifecycle documentation
No dormant contractor access inside sensitive citizen systems.

Continuous Identity Risk Intelligence
Advanced orchestration enables:
- Detection of unusual citizen data access patterns
- Identification of privilege creep across departments
- Automated remediation triggers
- Escalation of high-risk access decisions with preserved context
Identity risk becomes measurable, visible, and defensible across agencies.
Why This Matters to Public Sector Leadership

Stronger protection of citizen data

Reduced fraud and fund misuse

Improved audit and oversight defensibility

Consistent cross-agency policy enforcement

Clear accountability for access decisions

Lower risk of privilege abuse



