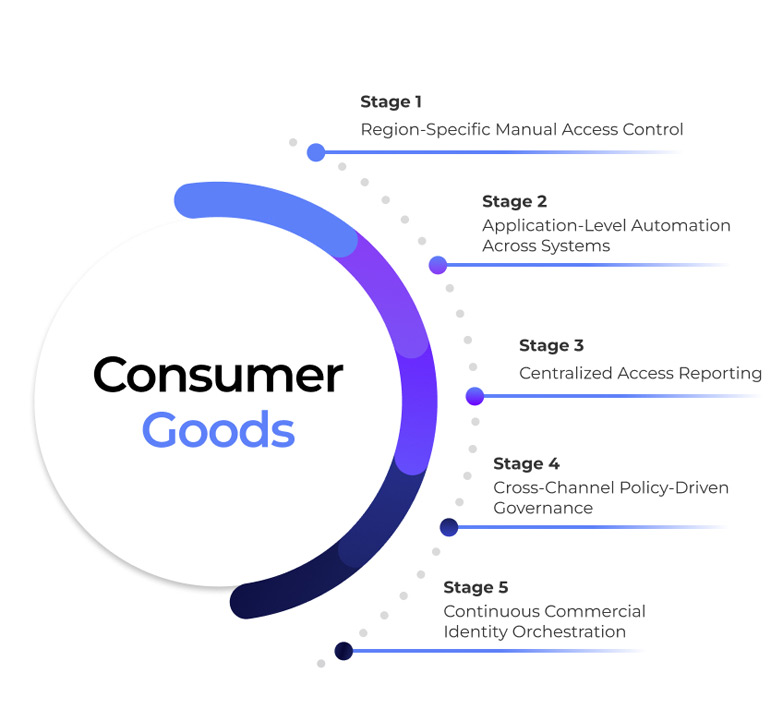
Consumer Goods
Protect brand, supply chain, and financial integrity without slowing distribution
How Orchestrated Identity Governance Is Reshaping Consumer Goods Enterprises

The Reality of Access Risk in Consumer Goods
Behind every demand forecast, pricing update, distributor transaction, and supplier payment lies identity in motion. Across consumer goods organizations, identity operates across manufacturing sites, regional warehouses, ERP platforms, sales systems, and third-party distribution partners. Sales teams shift territories, channel partners onboard and offboard, and supply chain roles change frequently. Yet access execution often lags behind operational change. Temporary partner access persists, role updates fail to synchronize across systems, and distributor permissions extend beyond contractual scope.
These are operational control gaps, not just IT inefficiencies. In consumer goods, unmanaged access can disrupt supply continuity, expose pricing and margin data, weaken compliance posture, and put brand reputation at risk across distributed markets.
The Core Challenges Consumer Goods Organizations Face
Distributed Workforce & Channel Complexity
- Consumer goods companies operate across corporate offices, factories, regional sales teams, distributors, and field representatives.
- Manual Joiner–Mover–Leaver processes cannot keep pace with transfers across geographies and business units.
- Access granted for regional or project-based roles often persists beyond assignment, increasing silent exposure.
Supply Chain & Partner Access Risk
- External distributors, logistics partners, contract manufacturers, and marketing agencies require system access.
- Over-privileged or unmanaged third-party identities can expose pricing models, inventory data, and supplier contracts.
- A single compromised partner account can disrupt supply chain continuity and financial reporting.
Segregation of Duties Across ERP & Finance
- In complex ERP environments, users may manage vendors, approve trade promotions, adjust pricing, and release payments.
- Conflicting access combinations are often discovered during audits or financial investigations.
- Without preventive SoD enforcement, fraud risk shifts from theoretical to operational.
Compliance & Reporting Pressure
- Consumer goods enterprises must align with SOX, GDPR, trade regulations, and regional financial compliance mandates.
- Auditors require clear evidence of access control over financial, supplier, and customer data.
- Traditional IGA produces static reports but lacks continuous enforcement across fast-moving supply chains.


Why Traditional IGA Falls Falls Short for Consumer Goods
Most IGA platforms were designed for centralized corporate structures with predictable roles.
Consumer goods requires:
- Cross-entity lifecycle governance
- Territory-aware access controls
- Time-bound distributor permissions
- ERP and supply chain orchestration
- Continuous enforcement aligned to distribution velocity

What Orchestrated Identity Enables in Consumer Goods
-
Lifecycle governance
-
Preventive control
-
SoD Enforcement
-
Third-Party Governance
-
Risk Intelligence

Lifecycle- Governed Workforce Access
When HR or regional assignments change:
- Access across ERP, sales platforms, supply chain, and finance systems updates automatically.
- Obsolete permissions are removed immediately.
- Role-based access remains aligned to territory and business responsibility.
No residual access across regions. No spreadsheet-driven cleanup.

Preventive Privileged Access Control
Orchestration enforces:
- Purpose-specific administrative access
- Time-bound elevation
- Automatic revocation post-task
- Full traceability of privileged decisions
Sensitive pricing, supplier, and financial systems remain controlled at scale.

Continuous Segregation of Duties Enforcement
Instead of discovering conflicts during audits:
- SoD risks are evaluated at request time.
- Conflicts across procurement, pricing, and finance modules are blocked before approval.
- Mitigations are enforced dynamically.
Risk is prevented, not reconciled later.

Third-Party & Distributor Identity Governance
Consumer goods ecosystems rely heavily on partners and distributors.
Orchestrated governance ensures:
- Channel-specific and time-bound access
- Automatic expiration aligned to contracts
- Clear sponsorship and ownership
- Audit-ready lifecycle documentation
No dormant distributor access inside core enterprise systems.

Continuous Identity Risk Intelligence
Advanced orchestration enables:
- Detection of unusual pricing or promotion activity
- Identification of privilege accumulation across regions
- Automated remediation triggers
- Escalation of supply chain risk with preserved context
Identity risk becomes visible across manufacturing, distribution, and finance.
Why This Matters to Consumer Goods Leadership

Reduced fraud and financial manipulation risk

Stronger supply chain integrity

Improved regulatory and audit posture

Lower exposure from partner ecosystems

Clear accountability for access decisions across regions



