Simplify Access Requests & Approvals
Make Every Access Decision Explicit, Accountable, and Defensible
Anugal replaces ticket-based access requests with governed authorization decisions so access is granted faster without weakening control or audit posture.
The Reality of Everyday Access Requests
Access requests are among the highest-volume identity transactions in an enterprise. They are triggered daily by onboarding, role changes, project assignments, vendor access, and emergency escalations. In large environments, hundreds or thousands of requests move through workflows each week. Despite this scale, many processes still rely on free-text submissions, email clarifications, ticket routing, and hierarchy-based
approvals. Managers often receive requests without structured context, clear entitlement mapping, or embedded policy validation.
Under pressure, speed takes precedence. Eligibility checks occur late. Segregation of Duties conflicts surface after provisioning. Business justification is inconsistently captured, creating silent access drift and audit exposure. Access requests are control decisions, not administrative actions. Without governance at request time, organizations lose clarity over why access was granted and whether it should have been approved.
Where Access Requests Break Down
Most enterprises struggle with access requests in predictable ways.
Ambiguous Request Intent
Free-form submissions obscure what access is actually being authorized.Misaligned Approval Ownership
Managers approve requests outside their accountability or expertise.Post-Provisioning Risk Detection
Eligibility and SoD violations are discovered after execution.
Over-Requesting as Default Behavior
Users select broad access to avoid future requests.Weak Decision Defensibility
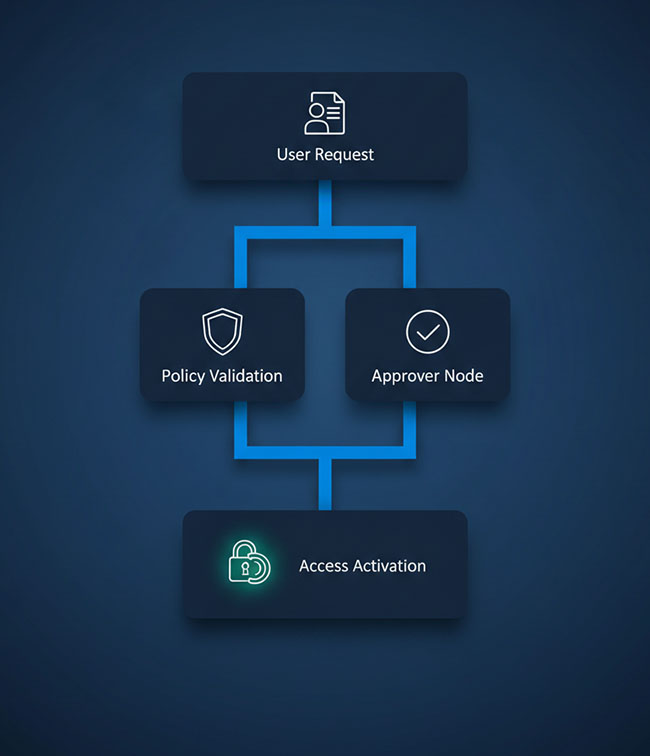
Audit logs confirm approval occurred — but not whether it was justified.The Anugal Difference: Requests as Authorization Decisions
Anugal treats every access request as a governed decision, not a service ticket.
Before a request reaches an approver, it is structured through role-based catalogs, evaluated against eligibility and policy rules, and enriched with context about risk and impact. Only valid, policy-compliant requests proceed.
Approvals are routed to the right owners, enforced by governance rules, and recorded as explainable decision events—creating clarity at runtime and defensibility later.


What This Enables Across the Request Lifecycle

Structured Requests Without Technical Friction
- Users request access in business terms, not entitlement codes.
- Role-based catalogs and guided selection ensure request intent is explicit, reducing misinterpretation and rework.
 Approvals Aligned to Real Ownership
Approvals Aligned to Real Ownership
- Decisions are made by those accountable for the access.
- Approval routing reflects access sensitivity, ownership, and policy—not just reporting hierarchy.

Policy Enforcement Before Access Is Granted
- Ineligible or risky access never reaches execution.
- Eligibility, SoD, and risk checks are enforced upfront, preventing downstream remediation.
 Decisions That Stand Up to Audit
Decisions That Stand Up to Audit
- Every approval is recorded with context.
- Who approved, under which policy, and why access was permitted is preserved beyond provisioning.
Why This Matters to the Business

- Faster access without bypassing governance
- Reduced remediation from incorrect or excessive provisioning
- Lower SoD and compliance exposure
- Clear accountability for authorization decisions
- Audit-ready evidence generated at decision time
Where Access Requests Fit in Your Governance Strategy
Governed access requests become the control point for:

Accurate access certifications

Effective SoD enforcement

Cleaner role and entitlement models

Defensible audit outcomes

Stronger least-privilege enforcement

Controlled privileged and third-party access



