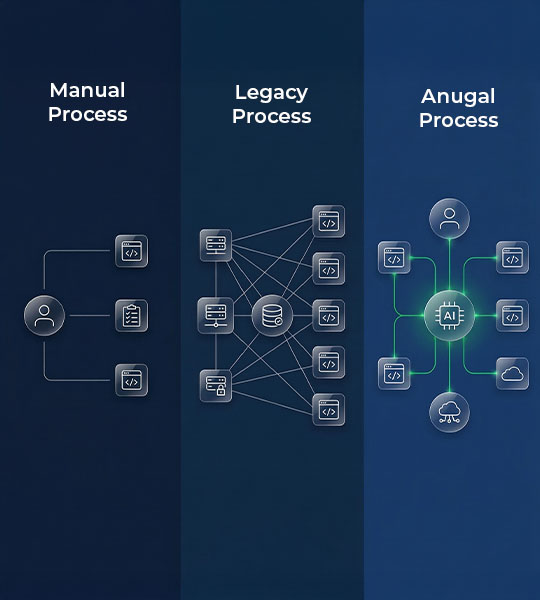
Augal vs Legacy vs Manual
Manual, Legacy IGA or Anugal: What Actually Scales in Enterprise IGA
Legacy IGA platforms define policies. Manual processes enforce them inconsistently. Anugal acts as an orchestration layer that coordinates identity actions across systems.
Move Identity Governance from Fragile
Processes to Controlled Execution
Most enterprises don’t intentionally choose between manual processes, legacy IGA platforms, or automation scripts, they gradually accumulate all three. Access requests flow through emails and ITSM tickets, certifications run in legacy tools, and custom scripts fill integration gaps across cloud and on-prem systems. Emergency access is handled through side channels, contractors are onboarded through parallel workflows. The result is fragmented control rather than a single system failure.
Over time, these disconnected layers create silent gaps: excess access that persists after role changes, Segregation of Duties conflicts that go undetected and orphaned accounts in unmanaged systems. Anugal closes these gaps by unifying governance, policy enforcement, and execution into a single orchestrated decision layer across the enterprise.
How Anugal Is Fundamentally Different
Anugal does not replace governance foundations. It extends governance into execution,
where most identity programs break. Instead of stopping at approval, Anugal orchestrates
identity actions across systems adapting to how access actually works in production
environments. Governance becomes continuous, operational, and scalable.
Dimension
- Primary Control Mechanism
- Scalability
- Speed of Change Handling
- Joiner–Mover–Leaver Accuracy
- Mover Access Correction
- Leaver Deprovisioning
- Legacy & Custom Applications
- SAP & ERP Role Complexity
- Third-Party & Contractor Access
- Privileged / Emergency Access
- Segregation of Duties (SoD)
- Access Reviews & Certifications
- Audit Evidence Quality
- Audit Readiness
- Operational Dependency
- Change Failure Handling
- Time-to-Value
- Future Expansion
Manual

- Human-driven follow-ups
- Breaks beyond small teams
- Slow, dependent on individuals
- Inconsistent
- Rarely enforced
- Task-dependent
- Spreadsheet-managed
- Manual interpretation
- Ad hoc, expiry missed
- Informal approvals
- Detected late
- Reconciliation exercise
- Reconstructed post-facto
- Reactive
- High on individuals
- Manual cleanup
- Immediate but fragile
- Not viable
Legacy
- Workflow + connectors
- Scales for standard apps
- Moderate, workflow-bound
- Partial, system-limited
- Often additive only
- Connector-dependent
- Frequently excluded
- Rigid role mapping
- Limited lifecycle control
- Separate tools required
- Checked at review time
- Periodic campaigns
- Approval-centric
- Periodic
- High on platform admins
- Partial rollback
- Long implementation cycles
- Costly and rigid
Anugal
- Policy-driven orchestration
- Scales across complex environments
- Event-driven and continuous
- End-to-end, lifecycle-aligned
- Obsolete access removed automatically
- Enforced across systems
- Governed via orchestration
- Context-aware execution
- Time-bound and enforced
- Governed within same model
- Prevented at request time
- Linked to real access state
- Decision + execution trace
- Continuous by default
- Reduced via orchestration
- Coordinated rollback & retry
- Fast, incremental rollout
- Designed for progressive coverage
Anugal’s Orchestration-Based Approach
Anugal acts as an intelligent orchestration layer across your identity landscape, connecting governance decisions directly to execution. It coordinates approvals, policy validation, and provisioning across disparate systems without disrupting existing access mechanisms. Instead of forcing architectural change, Anugal adapts to your current environment, integrating with legacy platforms, custom-built applications, and non-standard tools that traditional IGA solutions struggle to govern. By embedding policy enforcement and structured decision-making into real workflows, it ensures access is consistently controlled across IT, cloud, and business systems.
Over time, this orchestration reduces dependence on spreadsheets, emails, and manual follow-ups, replacing fragmented processes with governed, traceable execution at scale.
Agentic Assist Experience
AI-guided risk explanation, remediation suggestions, and policy assistance.
Access Experience
Unified interface for access requests, reviews, certifications, and audits.
Risk Intelligence
Visibility • Insights • Remediation Signals
Continuously analyzes permission, role, and entitlement risk across identities and systems
Access Decision Layer
Real-time Evaluation | Risk-Aware Enforcement | JIT
Evaluates access requests and changes in real time using policy, risk, and context.
Identity Control Domain
Lifecycle • Ownership • Entitlements
ILM | Role & entitlement governance | Non-employee access | Access reviews |
Password Management | Machine Identity
Anugal Core Engine
- Rules Engine
- Workflows
- Insights & Reporting
- Class aptent
- Execution Orchestration
Unified Identity Graph – One Model
Single correlated graph of identities, accounts, roles, permissions, and resources.
Connectivity & Extensibility layer
Data from applications, IAM, ITSM, security, and third-party sources
Shared Ecosystem Trust Signals
IAM | PAM | ITSM Security & Audit Platforms
Business Outcomes

Fewer manual access exceptions

Reduced audit remediation cycles

Stronger approval-to-enforcement linkage

Governance aligned to business change

Lower residual access risk

Improved decision accountability



