Self-Service Access Requests
Adopt a Self-service access that stands up to audit scrutiny
Get Policy-enforced access requests with approvals, traceability and audit-ready evidence.

Make access requests simple for users & defensible for audits
Self-service access requests in Anugal give users a clear, business-friendly way to request access through the Anugal UI, Copilot, or Microsoft Teams. Role-based catalogs and contextual recommendations help users request the right access without technical complexity.
Every request is governed by policy, routed for appropriate approvals, and fully logged. This reduces manual effort, prevents excessive access, and provides audit-ready evidence for every access decision.
Routine problem faced by Enterprises
Most of the time requests are raised without proper explanation resulting in audit risks and unnecessary access creep.

Unambiguous request intent
Free-form or loosely defined requests obscure what access is actually being authorized. s.
Approval without accountability
Decisions are made by hierarchy rather than by true access ownership.
Non-defensible audit trails
Approval records exist, but cannot explain why access was permitted.
Eligibility ignored at request time
Identities request access they should never be allowed to request.
Excessive access selection
Users default to broader access due to poor structuring of options.
How Anugal approach Access Requests?
Anugal governs access requests as authorization decisions, not service tickets. Request intent is structured before submission, eligibility is enforced before approval, and authority is assigned based on access impact. Every decision is recorded as a justification event, not just an approval action.
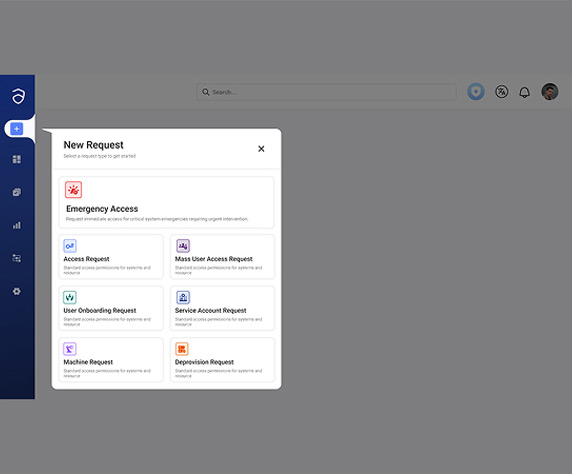
Business-Friendly Request Experience
Access requests are structured to reflect business intent rather than technical implementation.
- Users request access via Anugal UI, Copilot, or Microsoft Teams
- Guided selection replaces technical entitlement names with business terms
- Request intent is explicit and unambiguous
- Reduced dependency on IT to interpret access needs
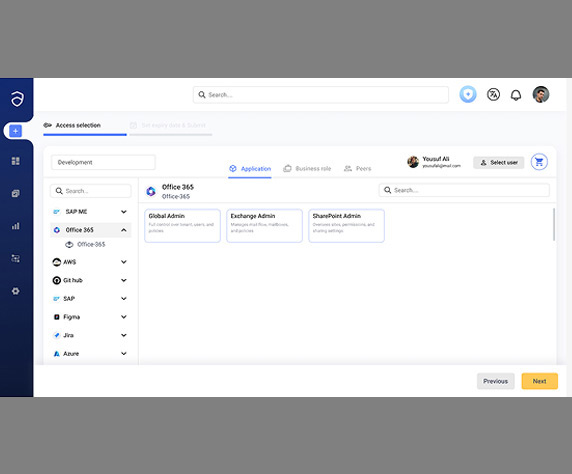
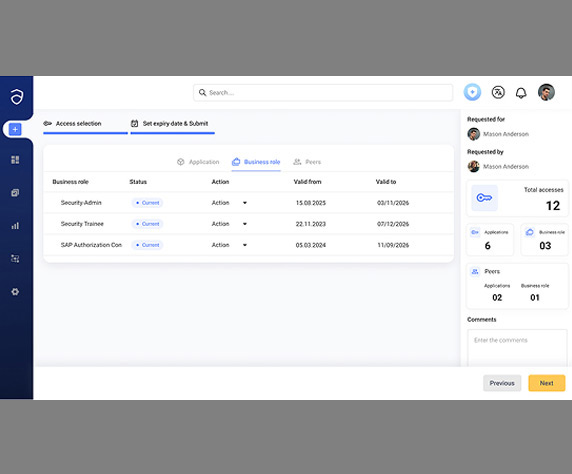
Role-Based Access Catalogs
Access options are constrained to approved and governed access models.
- Access presented as business roles and access packages
- Catalog entries are standardized and policy-approved
- Only eligible access is visible to each identity
- Ad-hoc entitlement selection is prevented at source
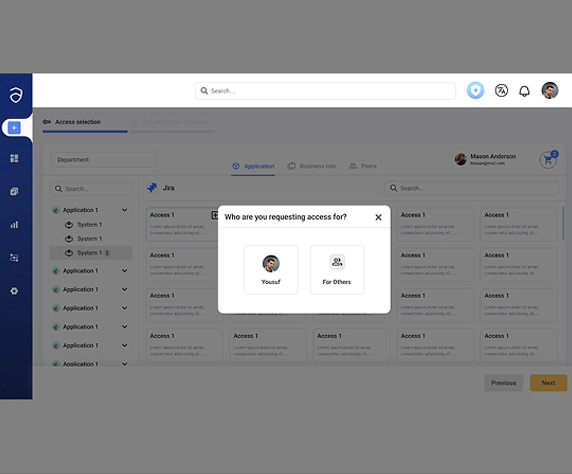
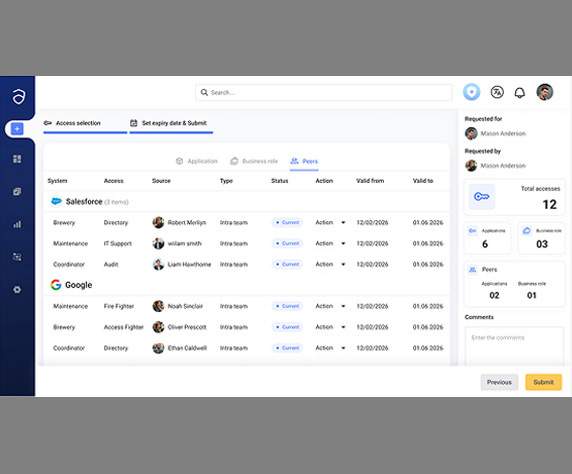
Peer-Based and Contextual Recommendations
Requests are informed by organizational access patterns without expanding scope.
- Visibility into access commonly held by peers in similar roles
- Requests aligned with established access norms
- Reduced trial-and-error submissions
- Higher first-time request accuracy
Policy-Driven Approval Controls
Authorization decisions are enforced through governance rules, not discretion.
- Approval routing based on role, risk, and access sensitivity
- Sensitive access triggers additional authorization layers
- Governance rules applied before approval
- No access granted outside defined policy boundaries
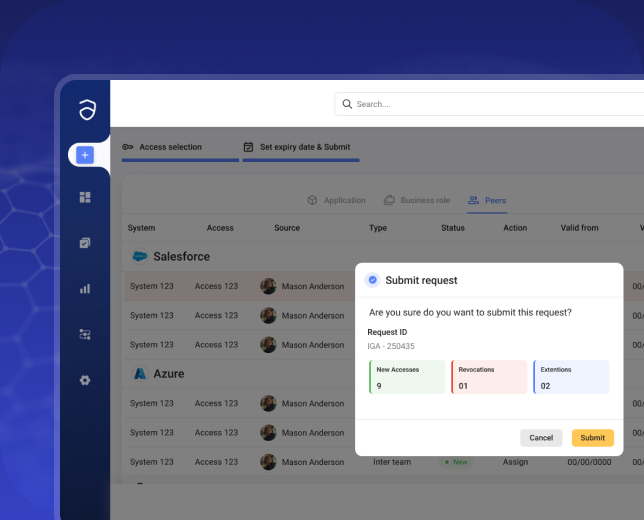
Request Tracking and Decision Transparency
Every access request produces a durable and explainable decision record.
- End-to-end visibility for requestors and approvers
- Clear record of who approved what and when
- Decision context preserved beyond provisioning
- Reduced follow-ups, escalations, and audit clarification
How Anugal Onboards Third-Party Identities in a Firm?
Anugal governs third-party identities by applying lifecycle-driven controls to non-employee access without disrupting operations. External users are onboarded through structured workflows, with access granted strictly based on business purpose, contract terms, and duration. Expiry and revocation are enforced automatically, while every access decision is logged to provide clear, audit-ready visibility.
Joiner Automation
- Access is provisioned directly from HR role and position data
- Employees start productive from day one without manual access requests
- Governance controls are enforced before any access is granted
- Access decisions are logged and traceable from the outset
Outcome:Faster productivity with controlled access
Mover Automation
- Access is recalculated whenever roles, departments, or locations change
- Excess and legacy entitlements are removed automatically
- Access reflects current responsibility, not historical roles
- Changes are governed and recorded as part of normal operations
Outcome: Continuous access alignment as roles evolve
Leaver Automation
- All user and privileged access is revoked immediately upon termination
- Orphaned and standing access is eliminated across systems
- Deprovisioning actions are consistent and verifiable
- Offboarding evidence is generated automatically
Outcome: Risk-free exits and audit-ready offboarding
Business impact of Anugal

Reduced IT effort interpreting and fulfilling access requests

Faster access delivery without weakening governance

Lower risk of excessive or inappropriate access

Clear, defensible audit evidence for every request

Fewer audit findings related to access justification