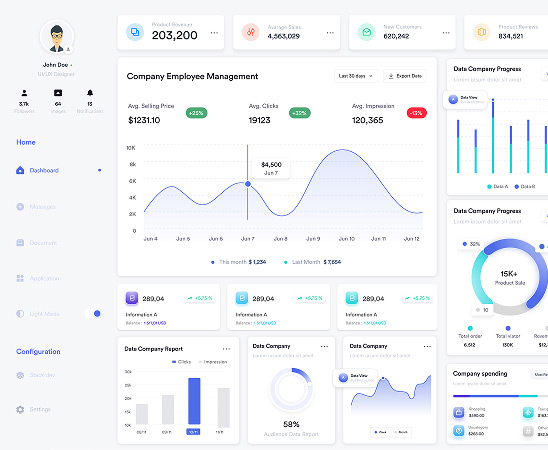
Machine & Non-Personal Identity Management
Govern non-human access with the same control and accountability as employee identities
Policy-driven lifecycle management for service accounts, bots and APIs with complete audit-readiness

Machine access is owned, governed, and continuously controlled.
Anugal governs identities that are not tied to individual employees, including service accounts, system users, background jobs, APIs, bots, and integration identities. These machine and non-personal identities operate continuously across systems, often with persistent and elevated access.
Without governed identity management, access is created for integrations and rarely revisited. Credentials remain active long after services change, rotation is inconsistent, and auditors struggle to trace purpose, ownership, and control. With a lifecycle-driven governance model, Anugal restores control by enforcing ownership, least-privilege access and continuous lifecycle controls
Why Machine and Non-Personal Identities Become a Control Gap?
Machine and non-personal identities exist to keep systems, integrations, and automated processes running. Unlike employee access, they are not anchored to HR lifecycles or business roles and are rarely reassessed once provisioned. As environments scale, these identities multiply rapidly and operate with limited visibility, ownership, or control.

Created outside workforce identity models
Service accounts, system users, and APIs are provisioned independently of HR or role-based governance.
Access persists by default
Credentials and permissions remain active even as systems, services, or integrations change.
Audit justification is weak
Purpose, ownership, rotation, and control for non-human access are difficult to demonstrate.
Ownership is unclear or undocumented
Responsibility for maintaining, rotating, or retiring non-human identities is often lost.
Privileges accumulate silently
Elevated access is granted to avoid operational disruption and is rarely reduced.
How Anugal Governs Machine & Non-Personal Identities?
Anugal applies a unified governance model to machine and non-personal identities by enforcing visibility, ownership, and policy-driven controls as standard conditions. Non-human identities are governed as first-class identity types, ensuring access remains purposeful, accountable, and auditable throughout its lifecycle.
Unified Visibility of Machine and Non-Personal Identities
All non-human identities are brought under a single, authoritative view.
- Consolidated inventory of service accounts, system users, APIs, bots, and integrations
- Identification of unmanaged and unknown non-personal identities
- Classification by system, function, and risk
- Visibility into access scope and usage

Ownership and Accountability Enforcement
Every machine and non-personal identity is explicitly owned and governed.
- Mandatory assignment of business and technical owners
- Clear accountability for access justification and review
- Prevention of orphaned or ownerless non-human accounts
- Defined responsibility during audits and investigations
Lifecycle Controls for Non-Human Access
Machine and non-personal identities are governed through controlled creation, change, and retirement.
- Structured onboarding, modification, and decommissioning
- Policy-enforced credential validity and rotation
- Automatic revocation when services, jobs, or integrations change
- Prevention of stale and abandoned non-human access


Least-Privilege Enforcement Across Systems
Non-human identities receive only the permissions required to function.
- Restricted access scope based on technical purpose
- Prevention of privilege sprawl across platforms
- Additional controls for sensitive and high-risk identities
- Consistent access boundaries over time
Evidence and Review Readiness
Non-human access remains explainable and reviewable at all times.
- Periodic certification of machine and non-personal access
- Visibility into usage, risk, and entitlement scope
- Recorded ownership, rotation, and access changes
- Audit-ready evidence without manual reconstruction
How Anugal Onboards Third-Party Identities in a Firm?
Anugal governs third-party identities by applying lifecycle-driven controls to non-employee access without disrupting operations. External users are onboarded through structured workflows, with access granted strictly based on business purpose, contract terms, and duration. Expiry and revocation are enforced automatically, while every access decision is logged to provide clear, audit-ready visibility.
Joiner Automation
- Access is provisioned directly from HR role and position data
- Employees start productive from day one without manual access requests
- Governance controls are enforced before any access is granted
- Access decisions are logged and traceable from the outset
Outcome:Faster productivity with controlled access
Mover Automation
- Access is recalculated whenever roles, departments, or locations change
- Excess and legacy entitlements are removed automatically
- Access reflects current responsibility, not historical roles
- Changes are governed and recorded as part of normal operations
Outcome: Continuous access alignment as roles evolve
Leaver Automation
- All user and privileged access is revoked immediately upon termination
- Orphaned and standing access is eliminated across systems
- Deprovisioning actions are consistent and verifiable
- Offboarding evidence is generated automatically
Outcome: Risk-free exits and audit-ready offboarding
Anugal’s impact on your business

Zero orphan machine identities across directories and ERPs

Reduced privileged access exposure from technical accounts

Lower attack surface by retiring unused service identities

Audit readiness with clear ownership and rotation records

Compliance alignment across SOX, GDPR, HIPAA, PCI, NIS2, DORA

Fewer integration failures caused by uncontrolled credential changes



